“Unique” – (adjective) being the only one of its kind; unlike anything else.
In data terms, “uniqueness” helps differentiate digital and physical objects. Using Unique Identifiers (UIDs) to distinguish between various objects helps enhance the selection process plus identify these objects more easily. UIDs improve and fasten database searches. UIDs help to decrease the length of programming-related code and assist organisations with creating more robust solutions and processes.
Before we look into common uses and best practices for using UIDs, let us first take a look at what UIDs are, what they are used for and what is their typical size or length.
What are UIDs commonly used for in data?
They are used for effective monitoring, analytics, inventory checking and tracking. With the help of UIDs, you can use alphanumeric characters to distinguish identical but interchangeable objects. Moreover, UIDs also assist in reducing errors in coding language and data entry.
What is a Unique Identifier (UIDs)?
A UID is a unique alphanumeric string of data used (generally) by the computer algorithm for any entity in the respective technology-based system. The entity could be a component, object or even a subcomponent. They are used to identify objects such as files, users, data records or other organisational data.
The algorithm normally adds UIDs incrementally. This process is often automatic and follows specific pre-defined rules. Some systems allow manual entry, which may cause inconsistencies or duplications in the long run. This also influences your ability to retrieve and search objects.
Physical interfaces also assist you in engaging with UIDs e.g. QR codes or Barcodes, IP addresses or DNS lookup names are just some common examples. UIDs also connect physical assets and digital systems e.g. SKUs – Stock Keeping Unit. Note, a SKU although “unique” may only be unique to a product line rather than an individual item within a line of product.
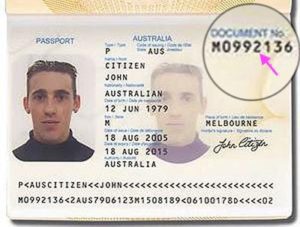
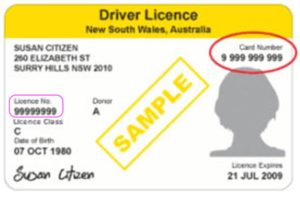
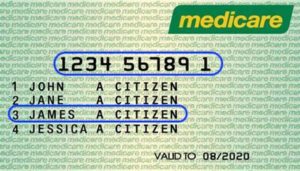
Here are a few key UIDs that identify you at a national and/or international level.
1/ Medicare number – there is only one unique number per card and you could be one a few numbers listed on that card. The card number combined with your number is your UID
e.g. 1234 56789 1 / 3 = James A Citizen. This is a nationally recognised Australian Government issued UID.
2/ Tax File Number (TFN) – there is only one TFN per Individual or Company. 9 digits in length. Your TFN is a Australian Tax Office issued UID.
3/ Passport number (Document No.) & Driver Licence – is the penultamate UIDs within Australia and internationally. Your passport number is a Federal government issued UID and is recognised locally and internationally when travelling. At a state-based level your driver licence number or card number is also a key UID. Your driver licence number or card number is not recognised internationally.
The Size or Length of the UID
Generally, the area of an organisation responsible for the system will pre-determine or set the length of UID. Organisations will often look to industry standards or perhaps other departments to set the appropriate length of UID. However, most systems come with a system generated UID, which can also be used.
Orgnisations may also use multiple UIDs for the one object but each should always lead back to that unique object, thing person e.g. mobile number, ABN number or email address could all be used as a way to identify an indvidual UID.
Common Forms of UIDs
UIDs can take different forms depending on their use and application. Let us look at the common examples of UID:
1. URI – Uniform Resource Identifier
A URI refers to a distinct identifier that helps to make content addressable over the internet. This is done through items such as applications, images, video and text.
2. UUID – Universal Unique Identifer
A UUID refers to a 128-bit alphanumeric number that is used to identify some entity or object over the internet.
3. GUID – Global Unique Identifier
A GUID is a unique number that Microsoft generates to develop a distinct identity for entities like a word document.
4. URL – Unifrom Resource Locator
A URL is a specific sort of URI that only targets Web Pages. Thereby, when a browser sends the requests for web pages, they are given to the users.
5. BIC – Bank Identifier Code
A BIC is a distinct identifier user for particular financial institutions such as banks, microbanks, etc.
6. UDID – Unique Device Identifier
A UDID is a unique string that is 40 characters long. It is assigned to specific Apple devices such iPad, iPhone or iPods.
7. SSI – Service Set Identifier
An SSI is a set of characters that distinctly names a WLAN.
Other than these common form UID examples, more simple ways to identify a user include their username, email address and mobile number.

Common Uses and Best Practice for UIDs
UID codes can be found in any digital systems. Let’s take a look at the common use cases and best practices that are used to employ UIDs. Note, although UIDs are unique to things or individuals, actual personal information pertaining to UIDs should be anonamised to protect against digital hacking. Unfortunately, we are seeing and experiencing more cases where highly personal information kept by large organisations are not being properly secured or anonymised correctly.
Website Registration
You can create a distinct password and username whenever you register on a website. It is then followed by the system creating a UID for all the registered users. The UID contains all the user attributes, including the password and username. This assists the organisations in tracking everything you do on the website and further helps them to provide you with personalised services. All the other activities and technical issues are to be referred to the Unique Identifiers.

Spreadsheets and Databases
Both spreadsheets and databases have a “primary key” field that helps them identify a cell or the record. The UID helps you to categorise records, filter them and get what is required.
For instance, you call your bank to discuss some transactions on your statement. There is a good chance the operator will ask for existing account number along with a series of secuity-based identification questions. The operator will use your account number to query their database with After completing the query, it should return your details from the corresponding database and display on their acreen. If you don’t have your account number handy they may also use your mobile phone number, email address or street address as another UID.
However, in this case, the account number or the “primary key” is their UID for you. This UID helps to distinguish yourself from other banking customers in their database. All your information also connects back to this ID for improved sorting and quick search results. Ultimately, this assists organisations in classifying their data and retrieving it within a few seconds or minutes.
Inventory Management and Supply Chain
A manufacturer in any organisation uses UIDs to mark and distinguish between their products. They use UIDs to track the company products through their lifecycle. It also assists retailers in administering inventories and provides better tracking of sales.

Patient Records.
Hospitals may often refer to a UID as the Patient ID, often found on your wrist tag. Hospitals develop a UID for every patient to track medications and treatment progress. It is the responsibility of the hospitals to safeguard the patient’s data against their UID. The patients maybe able access their records by visiting the hospital’s portal on their respective websites.

The Bottom Line
Simply put, most organisatons should or do have the need to implement Unique Identifiers. Unique Identifiers are created in many different ways but are often made up of alpha-numeric strings of data.
UIDs have many purposes from identifying objects, things or people. Simply put, there is a high chance that you have either used UIDs at your workplace to lookup information or as a customer when being asked to identify yourself or get an update on an order. At a more complex level UIDs exist in many different facets of life. In fact they are constantly used or generated second by second, minute by minute every, single, day when browsing the internet.
As technology keeps evolving, the use of UIDs will continue to increasing.
At Dovetail Group, we provide simple, yet effective revenue growth services and solutions to make everything work as it should.
Learn more.